The Dragonfly handshake in Wi-Fi is used to generate a unique Pairwise Master Key (PMK) for each pair of associated Wi-Fi Stations. This circumvents the problem of the same PMK being generated for all stations when using WPA2 personal security connection.
The Dragonfly handshake is based on the Diffie-Hellman (DH) handshake. The DH handshake uses a Prime number and a generator which are publicly exchanged alongwith private keys to compute a shared secret. The Diffie-hellman handshake can be best understood by a pictorial description as shown below (where MOD stands for modulo operation):
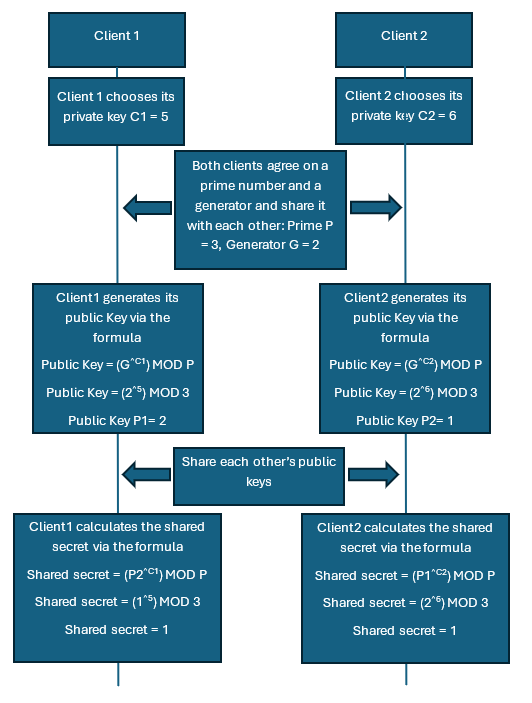
The numbers that I have chosen might not be the best for the algorithm, but the reader would get the general idea of the operation. Only the public value, prime and generator are sent out in air, the attacker cannot regenerate the shared secret key from just the three values. Since, each Wi-Fi client picks its own private randomly generated key, each independent connection will have a different shared secret (PMK) generated.
Dragonfly modifies the DH handshake by adding authentication to the handshake via a pre-shared secret. This in WPA3 is the pre-shared passphrase. Elliptic Cryptographic Curves (ECC) DH-19 group is mandatory in WPA3 defines the prime number for the DH handshake. The generator is derived from the password provided for the WPA3-personal network.
NOTE: WPA3 allows DH-groups 15 till 21. However, DH group 19 is mandatory and most often seen in implementation.
In the next article, we will see how the different parameters for the dragonfly exchange are computed in the SAE handshake.
Pingback: WPA3-Personal security changes | Hitch Hiker's Guide to Learning