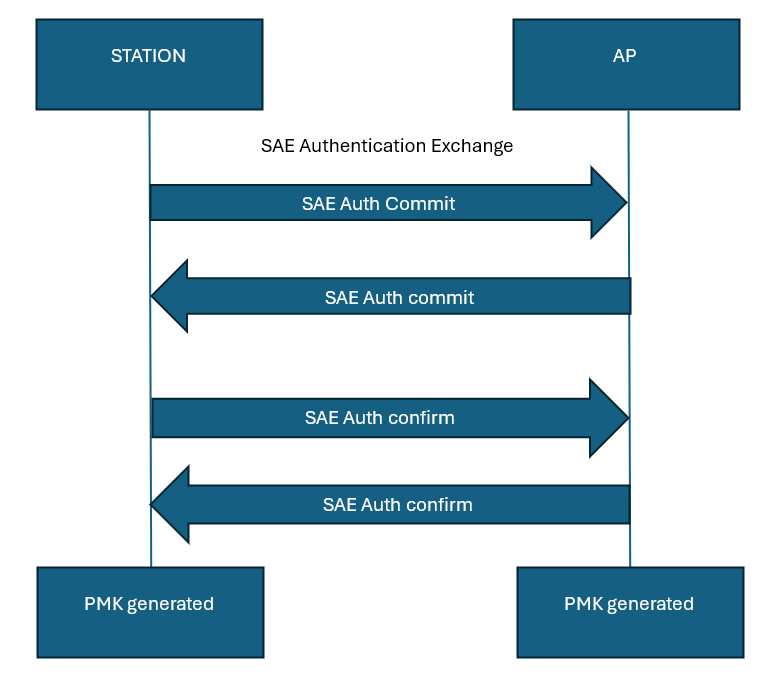
The SAE handshake is the 4-way authentication handshake that occurs instead of the earlier 2-way 802.11 authentication handshake. The 4-way handshake has two commit messages and two confirm messages in its 4-way handshake. The commit message sends out an scalar value, finite element and the DH group being used in the handshake. for reference, the 4-way handshake is provided below:
SAE which is based on the dragonfly handshake is a Password Authenticated Key Exchange (PAKE) algorithm. The Wi-Fi password is used to authenticate the key exchange. The salient steps in the SAE process are provided below:
- A password Element (PWE) is generated using either the older hunting and pecking loop or the newer Hash-to-Element method.
- In the Hash-to-Element method, A secret element (PT) is generated which is later used to obtain the PWE.
- Along with the PWE, two secret values (random value and mask) are generated
- The PWE and the secret values are used to generate the commit-scalar and the commit-element that are sent to the peer in the commit frame. The formula for computing the commit-scalar and the commit-element are provided below:
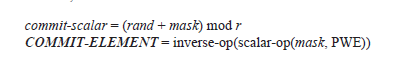
- Where in
- rand – random value generated
- mask – mask value generated
- r – prime order of the group
- scalar-op – an operation which generates a scalar value
- inverse-op – an operation which generates the inverse of the requested inputs
- Upon receipt of the scalar and commit elements, both peer’s verify the elements received
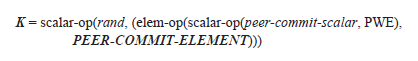
- Upon validating the scalar and commit elements, a shared secret element (K) is derived using the scalar and element received from the peer as shown below
- The secret element (K) is used to generate a secret value (k) whose entropy is later used to generate a keyseed, which is utilized to generate Pairwise Master Key (PMK) and SAE-Key Confirmation Key (SAE-KCK) as shown from the standard excerpt below
- The SAE-KCK is used for message integrity during the SAE-confirm messages
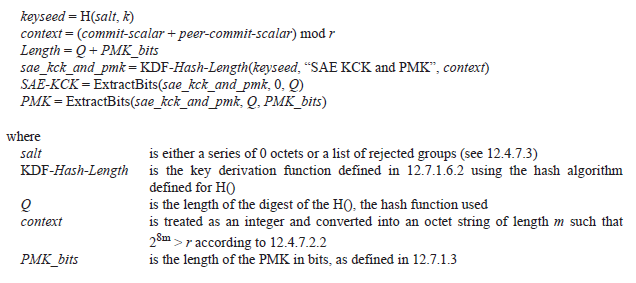
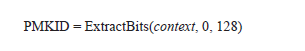
- The PMKID is also extracted from the context as shown below
- The confirm message is then constructed by both the involved station in the SAE handshake with the SAE-KCK, send-confirm current counter value, commit-scalar of station, commit-element of station, peer commit-scalar and commit-element of peer as inputs to a confirmation function
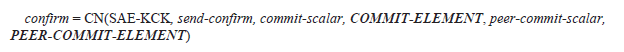
- The confirm message is sent over the air to one another by the peer entities engaging in the SAE handshake
- Upon receipt of the peer’s confirm message, a verifier function computes the expected confirmation message (peer-confirm) from the peer station to verify the confirmation message received is as expected
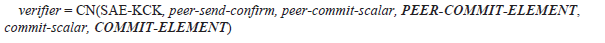
- If the verifier function value differs from the peer-confirm message received, then the SAE confirm message shall fail.
The computation of PWE along-with hunting and pecking method and H2E method are described in the 802.11-2024 standard (section 12.4). The interested reader is directed to look through the same.
Pingback: Diffie-Hellman (DH) handshake | Hitch Hiker's Guide to Learning