The WPA2-Personal Pairwise Master key generation is based on the Password Based Key Derivation Function version 2 (PBKDF2) (WPA2 PBKDF2 mechanism), which is later used to generate Unicast and group temporal keys used in encrypting traffic using the 4-way handshake. The PMK generated using PBKDF2 follows a hashing algorithm that creates the same Pairwise Master Key (PMK) every time for each of the clients in the network using the same password. The temporal keys generated using this PMK via PBKDF2 would vary for each client. However, It was observed that an attacker could capture the 4-way handshake and subject it to offline dictionary attacks and guess the PMK and the password as the PMK would be same for all clients.
The version of Dragonfly that is used in WPA3 is termed Simultaneous Authentication of Equals (SAE). WPA3-personal does not remove the password requirement and uses a password as in WPA2-Personal, however, it uses a stronger SAE algorithm to generate a unique PMK for each client. check this against WPA2, which generated the same PMK for each client using PBKDF2 algorithm.
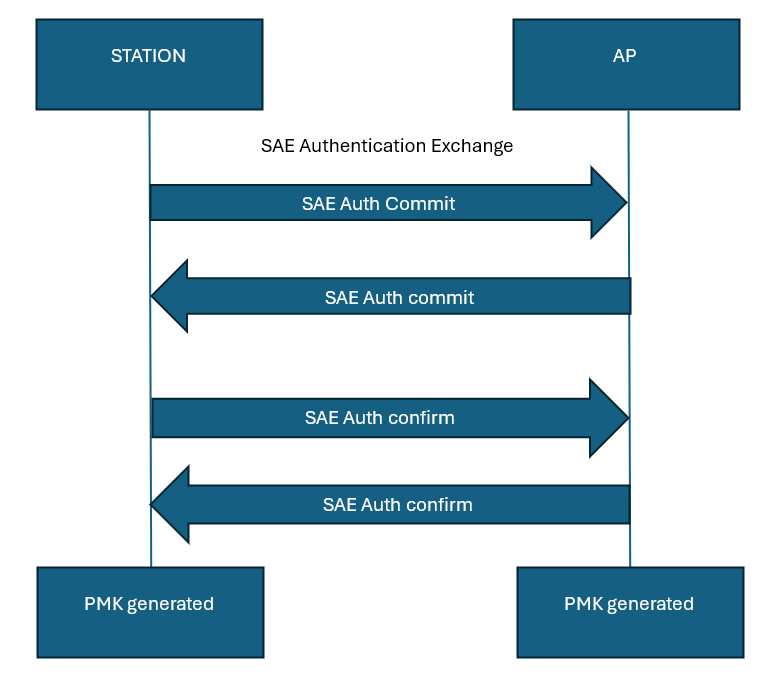
We will look at the detailed workings of the dragonfly algorithm in the next article. For reference, the SAE handshake generating the PMK at a top level is provided below:
Pingback: WPA3 security | Hitch Hiker's Guide to Learning