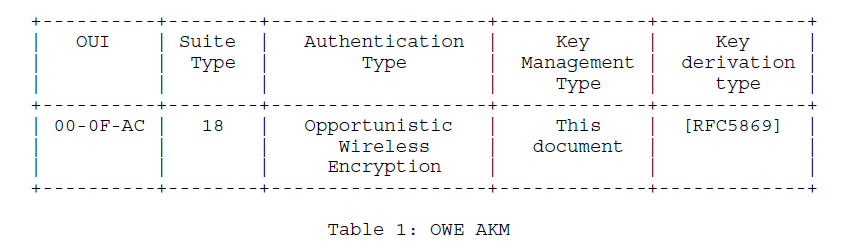
The Authentication key management (AKM) that is introduced for Opportunistic Wireless Encryption (OWE) is AKM type 18. The RFC 8110 describes OWE operation. The below excerpt from the RFC shows the OWE IE that is part of the RSN element. The Key management type is mentioned as “This document” to refer to RFC 8110. RFC 5869 describes – HMAC-based Extract-and-Expand Key Derivation Function (HKDF).
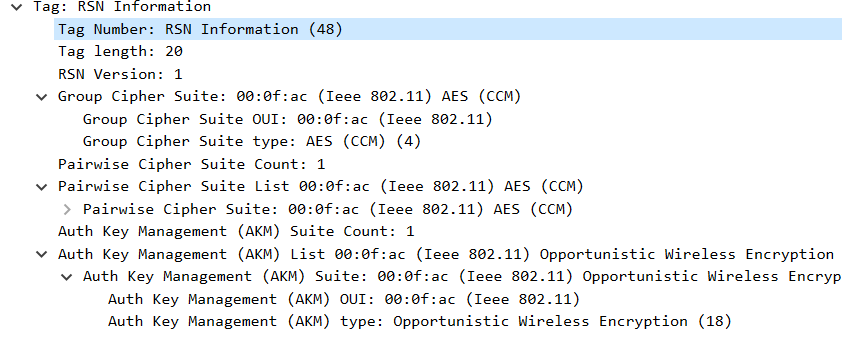
The Packet capture snippet for the above is provided below:
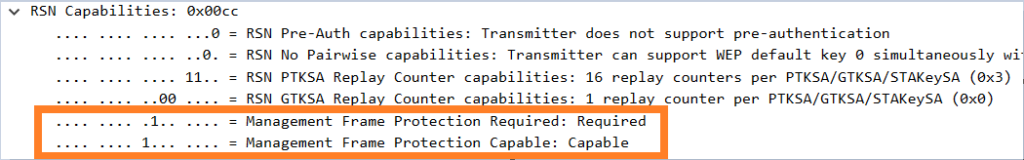
Most vendors enforce Management Frame protection (MFP) for OWE. The below settings are set
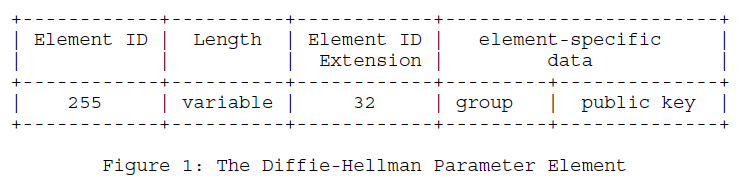
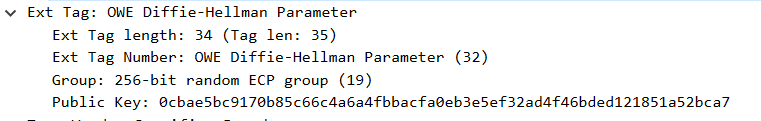
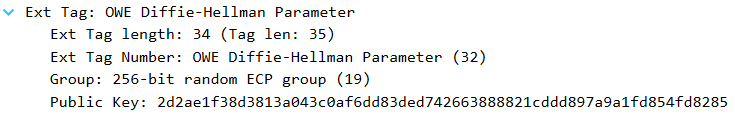
The OWE Diffie-Hellman (DH) parameter is sent out in the Association request and Association response frames by the Wi-Fi client and the Access point sending out their respective public keys to one another.
Association Request DH IE:
Association Response DH IE:
Once the Public keys are exchanged, the private keys of each station and the exchanged public keys are utilized to generate a shared secret. The operation to generate the shared secret is provided below from the RFC:
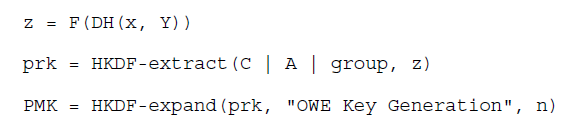
Where the parameters are as defined in RFC 8110:
- DH(X,Y) – For an elliptic curve, DH(x,Y) is the multiplication of point Y by the scalar value x, creating a point on the curve z; for finite field cryptography, DH(x,Y) is an exponentiation of element Y to the power of x (implied modulo a field defining prime, p) resulting in an element Z
- F(X) – An element-to-scalar mapping function. For an elliptic curve group, it takes a point on the curve and returns the x-coordinate; for a finite field element, it is the identity function, just returning the element itself
- In the above operation, Z is the point on the curve or the finite element
- HKDF-extract and HKDF-expand are defined in RFC 5869
- prk – Pseudorandom Root Key which is generated from concatenating below elements and then performing HKDF-extract operation on the concatenated element
- C – client public key
- A – AP public key
- Group – Group number (19 in this case)
- z – derived element from step 1
- The PMK (Pairwise Master Key) is then derived from the “prk” as shown in the formula above. It is passed as the salt value in the HKDF-expand operation and “n” is the bit-length of the digest produced by that hash algorithm.
The PMKID is also derived from the Client and Access point’s public keys as shown below:

Once the 802.11 association is successfully completed, the Access point initiates the 4-way handshake to the client using the PMK generated above.
Pingback: Opportunistic Wireless Encryption (OWE) | Hitch Hiker's Guide to Learning